Intro

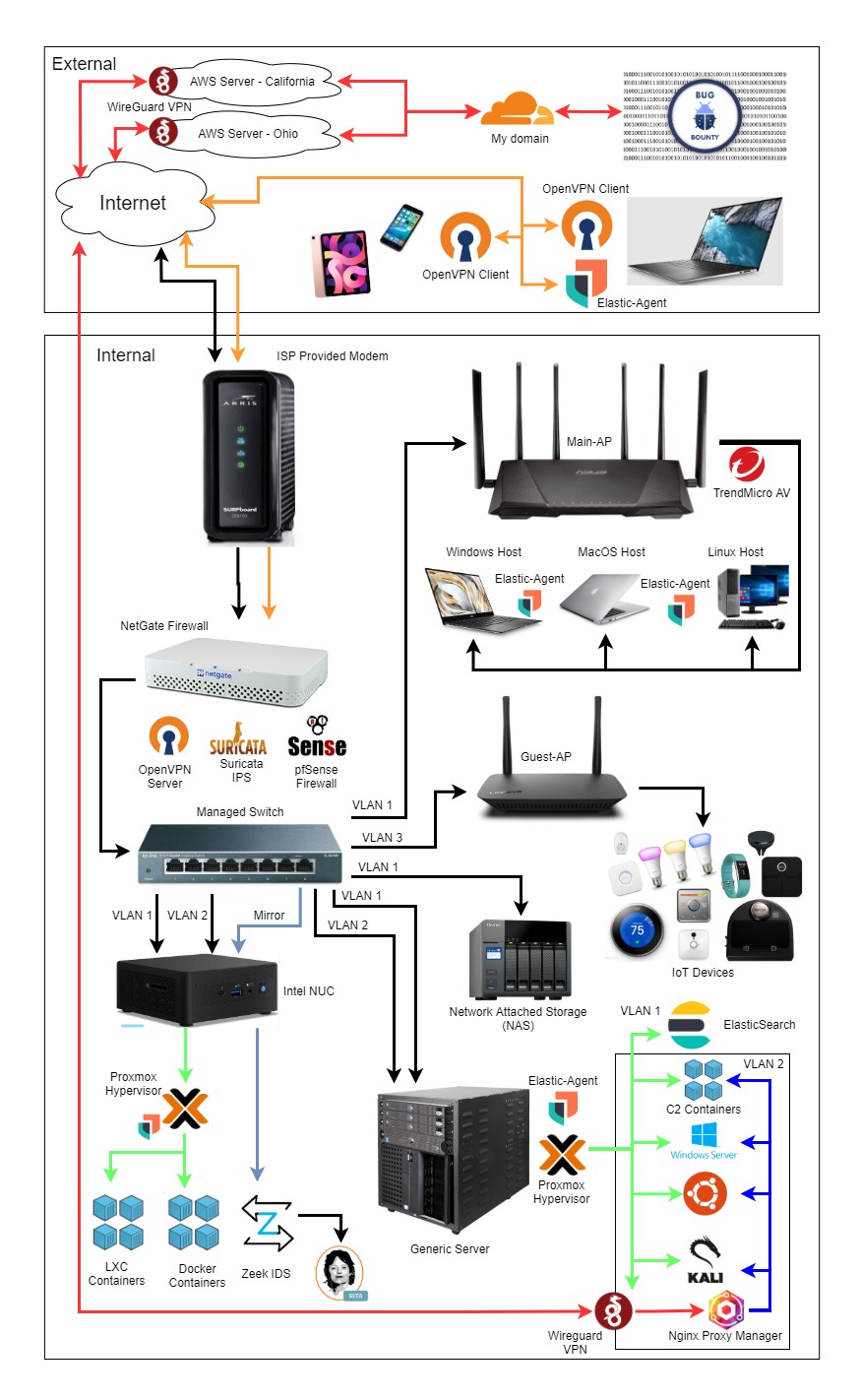
Hybrid cybersecurity learning focused on practical offensive and defensive security practices. My approach is based on understanding security behavior through real lab simulations.
My primary interest lies in penetration testing, vulnerability assessment,
and real-world attack simulations.
I build hands-on laboratory environments to study attack techniques, system monitoring workflows, and detection mechanisms.
I practice security analysis using real-world simulation scenarios.
I believe cybersecurity is best learned through practice —
every concept I study is implemented in a controlled lab environment.
Email: Tahireyvazli1988@gmail.com
Phone number: +99470 847 46 58;
Work
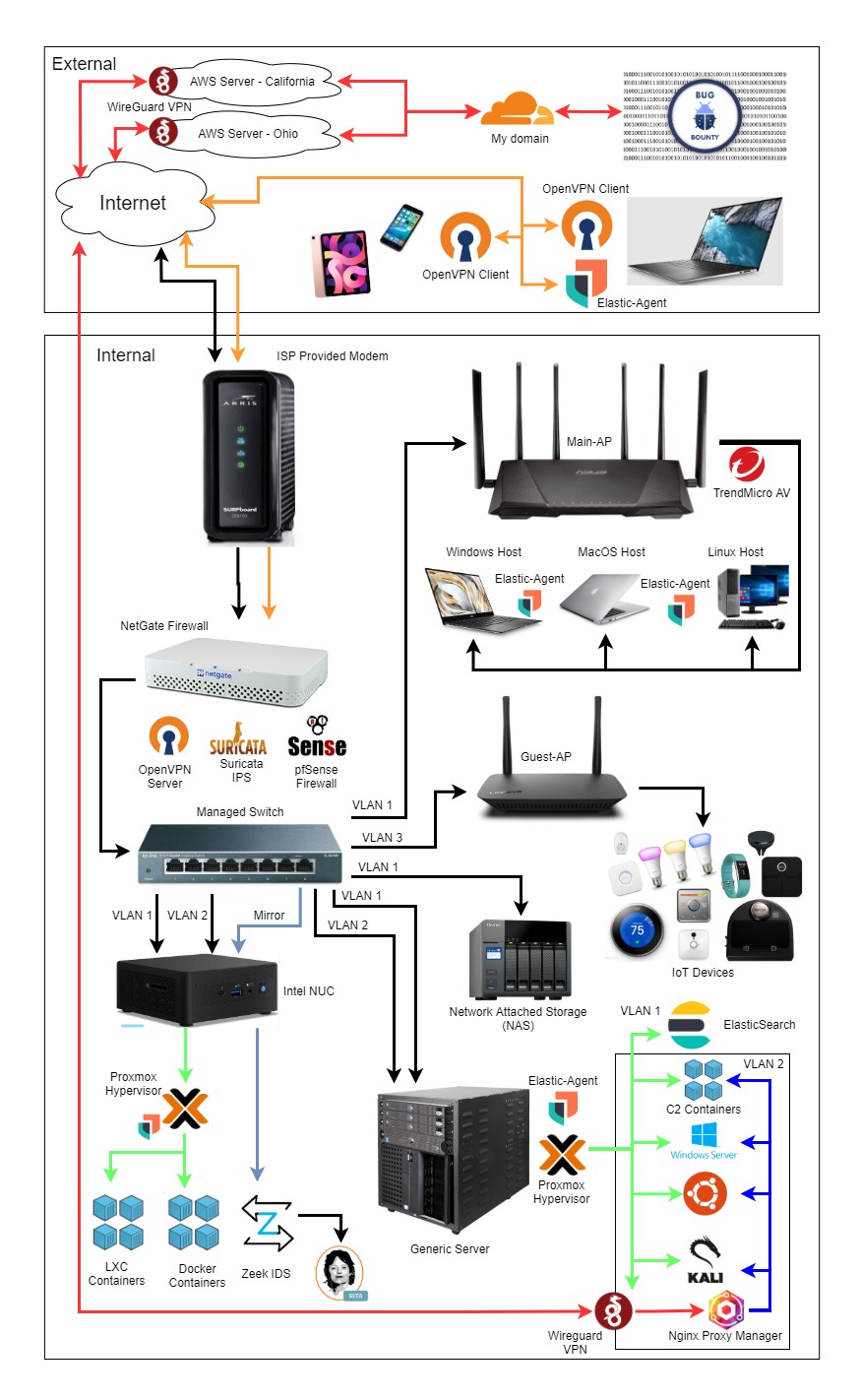
My work is focused on practical cybersecurity laboratory environments that simulate real-world attack and defense scenarios.
Offensive Security Practice:
- Vulnerability scanning and security assessment workflows
- Manual web application testing
- Exploit behavior understanding in controlled lab environments
- Network reconnaissance and enumeration practice
Defensive Security Practice:
- Security monitoring deployment using Wazuh and AlienVault
- Log analysis and alert investigation
- Intrusion detection configuration using Snort and Suricata
- Server hardening and access control tuning
All projects are developed in controlled laboratory conditions to study both attacker behavior and defensive response mechanisms.
About

Hybrid cybersecurity practitioner focused on understanding security systems from both offensive and defensive perspectives. My learning approach is based on practical laboratory experimentation and security behavior analysis.
I study how attacks operate at a technical level and design detection-oriented thinking models to improve defensive response understanding.
Technical learning areas include:
- Penetration testing fundamentals
- Network traffic analysis and monitoring
- SIEM configuration and alert optimization
- Linux security administration
My goal is to develop advanced cybersecurity engineering skills by combining attacker mindset analysis with defensive security intelligence.
Contact
Elements
Text
This is bold and this is strong. This is italic and this is emphasized.
This is superscript text and this is subscript text.
This is underlined and this is code: for (;;) { ... }. Finally, this is a link.
Heading Level 2
Heading Level 3
Heading Level 4
Heading Level 5
Heading Level 6
Blockquote
Fringilla nisl. Donec accumsan interdum nisi, quis tincidunt felis sagittis eget tempus euismod. Vestibulum ante ipsum primis in faucibus vestibulum. Blandit adipiscing eu felis iaculis volutpat ac adipiscing accumsan faucibus. Vestibulum ante ipsum primis in faucibus lorem ipsum dolor sit amet nullam adipiscing eu felis.
Preformatted
i = 0;
while (!deck.isInOrder()) {
print 'Iteration ' + i;
deck.shuffle();
i++;
}
print 'It took ' + i + ' iterations to sort the deck.';
Lists
Unordered
- Dolor pulvinar etiam.
- Sagittis adipiscing.
- Felis enim feugiat.
Alternate
- Dolor pulvinar etiam.
- Sagittis adipiscing.
- Felis enim feugiat.
Ordered
- Dolor pulvinar etiam.
- Etiam vel felis viverra.
- Felis enim feugiat.
- Dolor pulvinar etiam.
- Etiam vel felis lorem.
- Felis enim et feugiat.
Icons
Actions
Table
Default
| Name |
Description |
Price |
| Item One |
Ante turpis integer aliquet porttitor. |
29.99 |
| Item Two |
Vis ac commodo adipiscing arcu aliquet. |
19.99 |
| Item Three |
Morbi faucibus arcu accumsan lorem. |
29.99 |
| Item Four |
Vitae integer tempus condimentum. |
19.99 |
| Item Five |
Ante turpis integer aliquet porttitor. |
29.99 |
|
100.00 |
Alternate
| Name |
Description |
Price |
| Item One |
Ante turpis integer aliquet porttitor. |
29.99 |
| Item Two |
Vis ac commodo adipiscing arcu aliquet. |
19.99 |
| Item Three |
Morbi faucibus arcu accumsan lorem. |
29.99 |
| Item Four |
Vitae integer tempus condimentum. |
19.99 |
| Item Five |
Ante turpis integer aliquet porttitor. |
29.99 |
|
100.00 |